One of the criticisms levelled at cyber crisis simulations is the lack of tangible outcomes.
All too often the result of an expensive day table-topping is just another page in the swelling crisis bible or a wish list of new technology, as opposed to genuine advancements in the all-important human response.
In collaboration with Osterman, we asked 400 senior security leaders at large organizations for their opinions on crisis response. Our findings were clear: this mindset still pervades their efforts towards cyber crisis preparedness.
Setting clear priorities and objectives
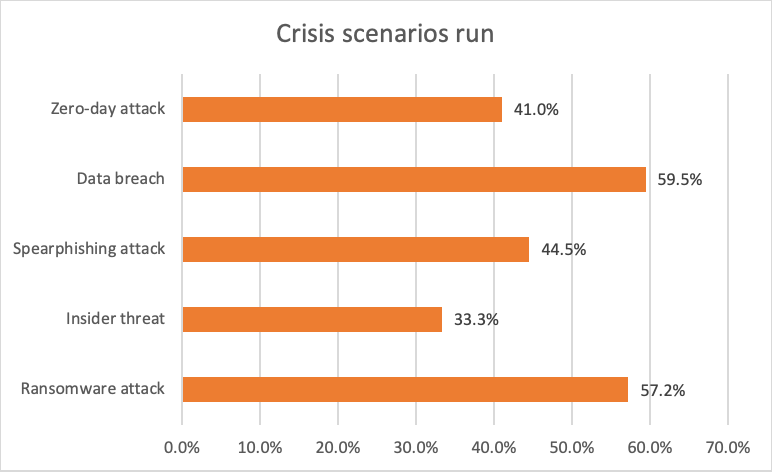
First, it’s important to understand which specific scenarios CISOs are using in their exercises, as this provides a baseline for understanding their objectives.
The graph below highlights five cybersecurity incidents that dominate tabletop exercises. Two of the more catastrophic scenarios – ransomware and data breach – clearly win the race.
These are not only the most high-profile cyber crises but also where effectiveness of human response and decision-making have the biggest impact on everything from share price to brand value. It’s no surprise then that security leaders want to ‘drill’ their teams’ capabilities here.
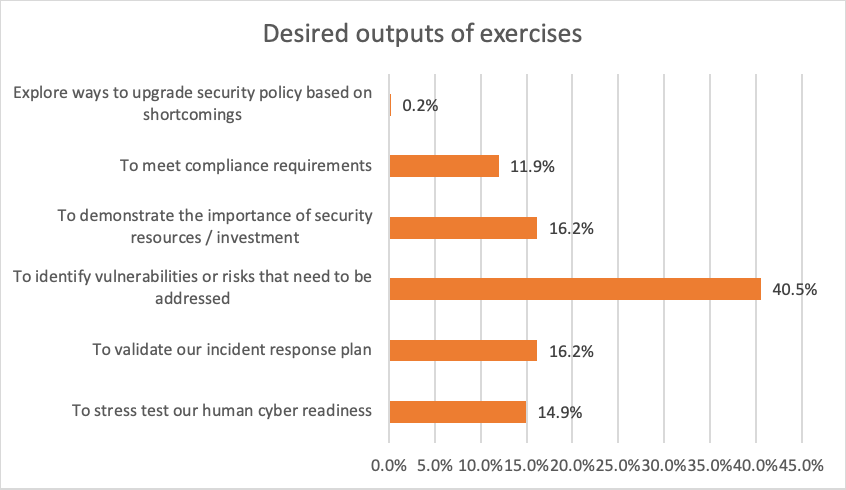
It is a little surprising, however, that only 15% of senior security leaders think stress testing human cyber readiness is one of the priority outcomes of such exercises (see graph below). In fact, the majority of respondents (41%) wanted to use such exercises as a way of identifying flaws in existing plans. While this may be a small distinction, it means almost three times as many people think processes are more important than people in crisis response. This is somewhat imbalanced when you consider what established experts think about the importance of building muscle memory in humans.
Outputs from cyber crisis exercises
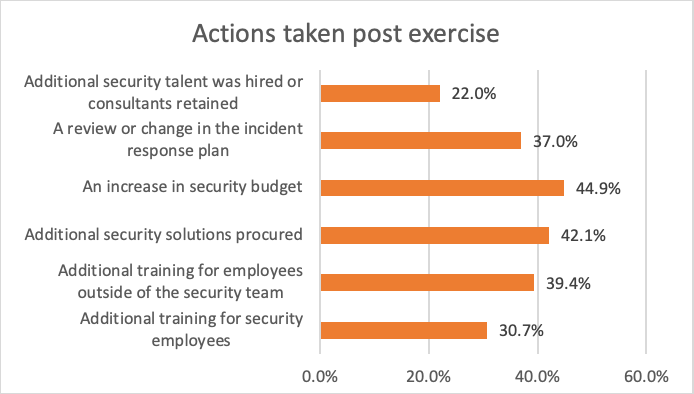
As anyone who has been involved in a real cyber crisis knows, learning from mistakes made while under attack and using these to make tangible changes is crucial to evolving a business’s security posture. For this reason, it’s heartening to see that the majority of people questioned (63%) said crisis exercises generated follow-on actions within the business they represented.
The most common of these outcomes was to secure more budget (45%). This is a positive sign that boards are prioritizing cyber risk and are willing to be proactive in securing their organizations against attack. Interestingly, a combined total of 92% decided to invest in people as a result of exercising by either providing additional training for existing employees or hiring new talent.
At Immersive Labs, we believe continuous human development is vital to an effective cyber crisis response. Only by running regular micro-drills with a cross section of technical and non-technical specialists can an organization develop the necessary muscle memory to respond effectively when the worst happens. But this is difficult, especially when relying on legacy training approaches based on lengthy tabletop exercises that require a significant amount of money and time.
To address this situation, we have launched Cyber Crisis Simulator, a platform that makes crisis simulations simple to set up and run. Cyber Crisis Simulator throws decision-makers into a variety of emerging attack scenarios within a browser, encouraging them to make collaborative decisions that have a real-time impact on share price and reputational value.
Published
17 August 2020
Cyber Crisis Response: Fit for today’s threat landscape?